Popping LFI on Android Apps with over 21M+ Downloads
Hello everyone! Hope you’re doing good.
This post is related to a LFI I found on three Android Applications namely:
- ASR Voice Recorder
- SCR Screen Recorder
- ACR Call Recorder
These are a set of recording apps made by NLL Apps, UK. Initially, this LFI was found on ASR Voice Recorder, which is an app used to record audio in various lossless formats, irrespective of how potato your device is, but was later found on all the three apps. As I report this, the issues have been patched.
Many low end Android devices ship with noise cancellation activated and enabled by default. This, is a feature when you’re on a voice call, but a big issue when you’re recording audio on your phone. While recording acoustic music on your phone, such as a guitar/violin, the higher frequencies get capped when noise cancellation is activated and I was unable to find a way.
Looking for a solution to this, I found ASR Recorder. Using this, you can customize the recording parameters such as the bitrate, format, stereo/mono and even choose which mic you wish to use.
How was the bug found?
Been using this app for almost a year, I was looking for an efficient way to transfer recordings to my laptop and share a small recording with everyone on WMD 2020.
Turns out, there is a feature which opens up a port on the Android phone, and on navigating to the address (http://ip_of_your_android_device:port/), one can browse the recordings and download them.
Here’s what it looks like:

Now, if I click on any recording, it gets downloaded, which is indeed the feature,
but here’s the catch,
what if I actually see the entire path from where the file is being downloaded? Hovering over the directory listing, I see the actual request link:
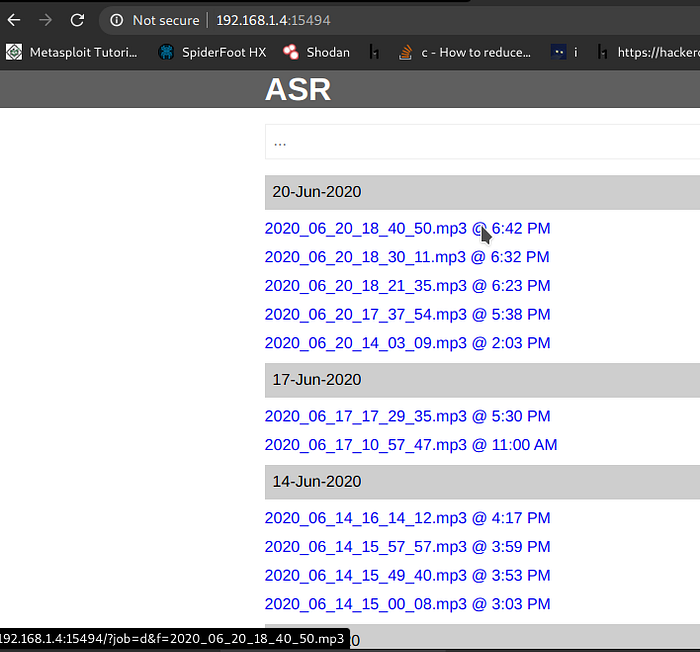
http://192.168.1.4:11586/?job=d&f=2020_06_20_18_40_50.mp3
Note the parameter f.
I go ahead to see if I can download any other file which is outside the recordings folder. Let’s say, a file Books.pdf which is in the Download folder.
*at this point of time, I chose to use Burp, for a better request-response view*
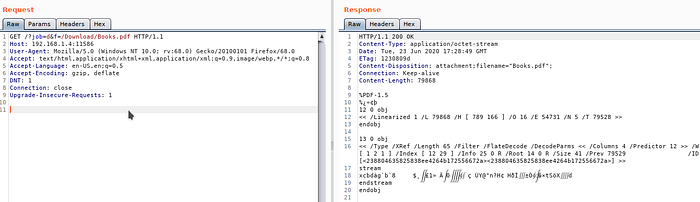
As of now:
- One can access other files on the Storage, provided the path to the file is known
- Once the Wi-Fi Access Activity is visited, it remains open in the background. So, one can simply do an nmap scan, find the port and wreak havoc.
- The files are straight away downloaded if they exist, else, we get a 404. If we try to view the directory structure, we get a 500.
Cool.
So basically, we need to know the path of the file we need to download. On accessing the most favorite of all , /etc/passwd file using /../../../../../../etc/passwd as the payload, this was returned:
#
# THIS IS AN AUTOGENERATED FILE! DO NOT MODIFY!
#
# Defined in file: “device/qcom/common/config.fs”
qti_diag::2901:2901::/:/system/bin/sh
rfs::2903:2903::/:/system/bin/sh
rfs_shared::2904:2904::/:/system/bin/sh
eg. Files in the ‘/WhatsApp/Media/WhatsApp Images’ are named as IMG-YYYYMMDD-WAXXXX.jpg, where XXXX are digits.
You know where this is going, right?
You can now download all the WhatsApp Images from your device(or the victim device) (provided that they have WhatsApp installed) by simply enumerating the digits in XXXX field from 0000 to 9999 using Burp Intruder.
And to do this, the victim has to be on the same WIFI and needs to only open the Wi-Fi Access on ASR Recorder. And if the victim device is rooted, you can get a lot of stuff and things can be then, pretty bad.
NLL Apps officially don’t have a responsible disclosure policy. But when I found this in a non-intrusive way and the potential impact of such a popular app, informing them was necessary.
On finding this on the other 2 Apps as well, as they were from the same vendor with over 21M+ downloads together, I contacted them via Twitter and they were pretty quick in responding and fixing the same in the update.
21st June 6:25PM IST — Issue reported via Twitter
23rd June 9:01PM IST — Issue fixed, as confirmed by the Author
Developers at NLL Apps were kind enough to help me with a few promo codes of their apps, so I now have the premium versions :p
What else could I have got on the World Music Day anyway :’)
.
.
.
Here’s a small clip that I recorded later in the day
Thank you for your time and I will try to keep up with this journey. Any suggestions, feedback, criticisms would make me a better individual tomorrow. A full-time learner trying out things, in all possible ways.
~Just a tiny speck of dust trying his shot.